The tests consist of two parts:
Two test computers:
-
Platform - Asus Terminator
-
Processor - VIA C3 866MHz
-
LAN adapter - Intel Pro/100+ Management Adapter
-
Memory - 128MB SDRAM
-
Hard drive - Maxtor 20GB
-
OS - Linux 2.4.21 (or higher)
Performance test
One PC is on the local network (and it's connected to the router's local
port), the other is on the outer one (connected to the WAN port). A tested
device is placed between them. Then the traffic generators start up, and
measurements are taken. This is how the router's performance is measured.
A switch integrated into the device is not tested as its speed is higher
than the routing rate.
Iperf v1.7 is used for traffic generation ad measurements. Each test
(30 sec long) runs 20 times, with the best and average results written
down afterwards.
The other utility is netPIPE v3.5. It generates traffic with gradually
increasing data packets (a packet of the size N is transferred several
times, the number of transfers is inversely proportional to its size but
not less than 7). Packets get transferred forth and back in series (not
simultaneously). This scheme shows to what degree the channel is used depending
on the size of data transferred.
Iperf parameters:
client: iperf -c $IP -w 64K -l 24K -t 30
server: iperf -s -m -w 64K -l 24K
netPIPE parameters:
receiver: NTtcp -b 65535 -o logfile
transmitter: NTtcp -b 65535 -o logfile -h $IP
Performance
Iperf.
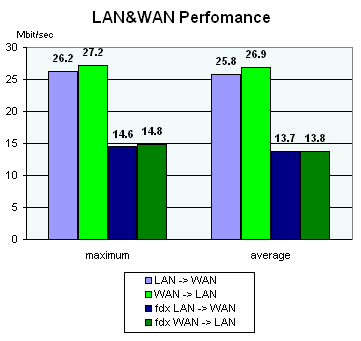
The program generates a one-way TCP traffic that is why all three possible
situations are modeled.
-
Traffic transfer from LAN to WAN (LAN2WAN);
-
Traffic transfer from WAN to LAN (WAN2LAN);
-
Both-way traffic transfer (fdx WAN&WAN);
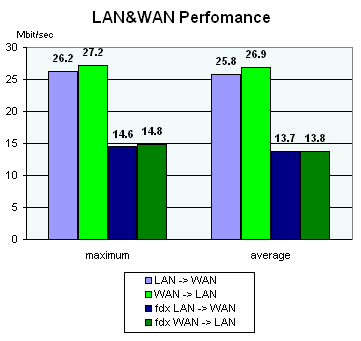
On the figure above you can see test results of one of the routers. The
maximum score is on the left, and the average value (based on 20 values
obtained) is on the right.
netPIPE.
The program generates a traffic by the Ping Pong method. That is why
the data rate remains the same irrespective of on which side the netPIPE
client is and where the server is.
Beside the diagram you can see the maximum fixed data rate.
Security
For this test we use the latest version of the freeware network security
scanner Nessus (at the moment it is v1.2.7). An external WAN port is scanned
with all available plugins from the list.
In the end we get a brief
report (without the list of configuration of the current scanning) and
a full
report generated by Nessus. But even if Nessus finds no vulnerability (or
the degree of risk is very low) it doesn't mean everything is OK, because
it can appear at any moment. But we can be sure that the programmers paid
due attention to this aspect of operation of the device.
Write a comment below. No registration needed!